On 25 February, Russian troops blew up a gas pipeline near Kharkiv, Ukraine’s second-largest city. Russia claims to have control over Chernobyl nuclear power plant, reviving memories of the tragic accident in 1986 whose after-effects can still be felt, only 100km away from Kyiv. On 2 March, Russia claimed to have taken control of the area surrounding the 5.7GW nuclear power plant in Zaporizhzhia, Europe’s largest. A fire broke out at the power plant a day after, despite crowds of unarmed Ukrainian citizens lining up to protect the installation.
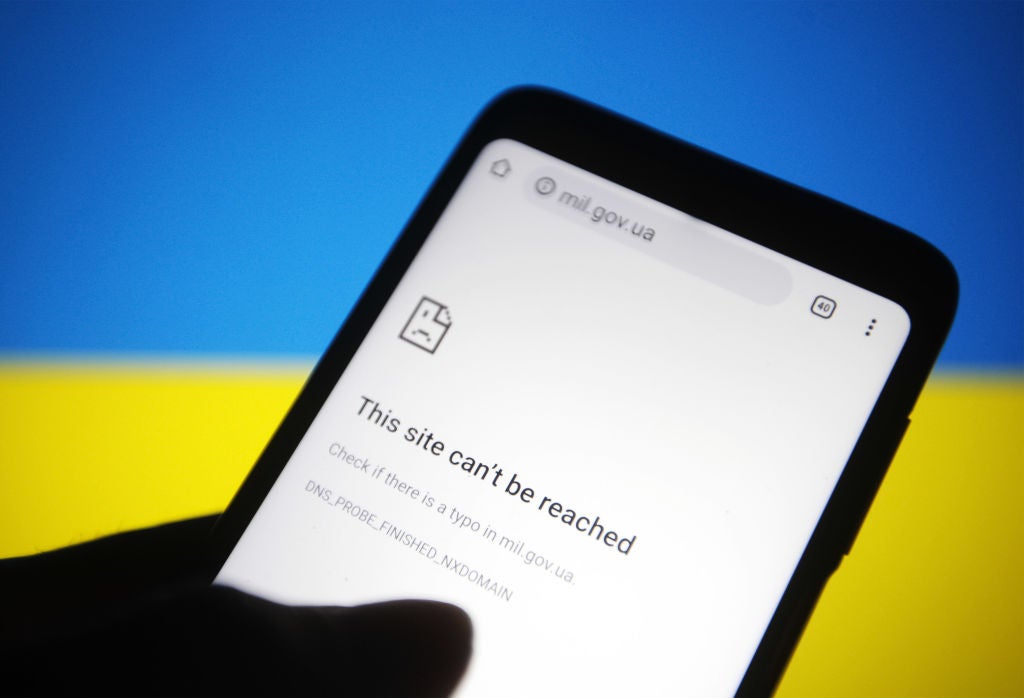
On top of the physical threat, the fear of cyberattacks hangs over Ukraine. Kyiv was the subject of a major cyberattack in 2015. On 1 March, Microsoft reported cyberattacks just before Russian tanks and missiles hit several Ukrainian cities, using a new malware denominated ‘FoxBlade’. “As tanks rolled into Ukraine, so did malware,” tweeted Indonesian author and human rights activist Andreas Harsono.
As tensions between Russia and Ukraine began to rise, much of the attention was focused on security of energy supply, notably the EU’s dependence on Russian gas.
However, the war on Ukraine is also exposing the need to preserve and support critical energy infrastructure, from power plants and power grids to oil and gas pipelines, as the ‘toolbox’ of hybrid warfare tactics grows.
“Hybrid tactics are a combination of conventional and non-conventional tools, hidden and evident, online and physical, aimed at destabilising, disorienting people and spreading panic, in the case of Ukraine today,” says Sofiia Shevchuk, an independent security and foreign policy expert. “[The] energy sector here is a ‘sweet spot’ considering it is a key to living and survival of Ukrainians.

US Tariffs are shifting - will you react or anticipate?
Don’t let policy changes catch you off guard. Stay proactive with real-time data and expert analysis.
By GlobalData“Areas surrounding energy assets seized by Russians are at a huge risk of facing a humanitarian catastrophe, with no water, food, power or heat,” she adds.
The cascading nature of energy projects could mean massive consequences for other critical infrastructure, if they are attacked. While Europe has become better prepared and more resilient to cyberattacks, hackers and state-sponsored groups pose a threat here too.
Fear for Ukraine’s nuclear plants
The attack on the gas pipeline near Kharkiv on 25 February left more than 40,000 residents in the area without gas. “A targeted attack on critical infrastructure is a terrorist act against the civilian population of Ukraine,” said Serhiy Makogon, CEO of the Gas Transmission System Operator of Ukraine.
The International Atomic Energy Agency has raised the alarm over the safety of Ukraine’s nuclear plants. Its director-general Rafael Mariano Grossi has repeatedly stressed that any military or other action that could threaten the safety or security of Ukraine’s nuclear power plants “must be avoided”.
“There might be warfare on the ground and nuclear power plants could be part of combat zones," Frank Umbach, research director at the European Centre for Climate, Energy and Resource Security, at King's College London, told Energy Monitor. "Like in Chernobyl, for instance, which is located in a transit area to get to Kyiv. The physical security of nuclear power stations is certainly something that is concerning."
Maxim Timchenko, CEO of DTEK, the largest private investor in Ukraine’s energy industry, told a briefing for journalists on 26 February that the country’s electricity grid was still stable, but that one of DTEK’s coal plants in occupied Luhansk is offline.
According to news agency Interfax, Russian forces also seized a hydropower plant in Kyiv and another one in Nova Kakhovna, in the country’s south, raising the alarm over possible major blackouts. The State Emergency Service of Ukraine also warned of two oil depots in Zhytomyr on fire on 7 March, after Russian air strikes.
While Ukraine has lived under the threat of cyberattacks for many years, Russia has opted for causing physical damage and full-blown military attacks to Ukrainian infrastructure since the invasion started. “In this case, you use cyberattacks when you want to be silent, when you don't want to be identified, and want to be effective," says Vytautas Butrimas, a cybersecurity expert with the Vilnius-based Nato Energy Security Centre of Excellence. "In this case, [Russia] doesn't care about hiding, they don't care if the world sees that they are launching an attack.
“It is a lot easier than spending months trying to break into a control system through a cyberattack,” Butrimas adds.
A ‘test field’ for cyberattacks
Ukraine faced a major cyberattack on 23 December 2015, which left roughly 230,000 households without electricity for up to six hours. The attack was attributed to a Kremlin-sponsored hacker group, and it was said to be the first publicly acknowledged successful cyberattack on a power grid.
“That was an attack that started around one-and-a-half years before [it happened], by inserting viruses into Ukraine’s electricity grid to detect its vulnerabilities," says Umbach. "The real attack only came later, by disrupting power supply."
That was a major turning point for efforts in Ukraine – and the EU – to make their energy systems more resilient. Since 2015, Ukraine has become a ‘test field’ for Russian cyberattacks: experts believe Russian hackers have tested new modes of attack and viruses on Ukrainian infrastructure, with an eye on potentially hitting EU countries too.
“[European] experts have always looked very closely at what is happening in Ukraine because what is happening there could happen on our side too, in case of a major conflict with Russia – which we now have,” Umbach says.
“We fear Russia’s cyberattacks have intensified, and not just in Ukraine, but we also fear major cyberattacks on critical infrastructures and critical energy infrastructures will intensify in the in the weeks and months ahead,” he adds.
Despite numerous efforts to counter them, the number of cyberattacks in the EU has been on the rise in recent years. The EU Agency for Cybersecurity's 2021 Threat Landscape report said that “cybersecurity attacks have continued to increase through the years 2020 and 2021, not only in terms of vectors and numbers but also in terms of their impact”, with ransomware becoming the main threat in the past couple of years.
Decentralisation and resilience
If Ukraine could restore its power generation in a relatively short period of time in 2015, it was largely because its energy system was not as digitalised as in most of the EU. “It could get restored relatively quickly by pushing some buttons, something that western Europe, with a much more digitalised and centralised system, would not be able to do,” says Umbach.
Europe’s power system has become more decentralised as the EU built up its renewable energy capacity. One welcome side effect is greater resilience against a major cyberattack. Moreover, as the energy and digital transitions become more intertwined, the European Commission has made significant efforts to integrate cybersecurity into its energy policies.
The EU’s 2020 cybersecurity strategy includes provisions on the security and resilience of the bloc’s power system. In parallel, a 2019 recommendation on cybersecurity in the EU’s energy system pointed out that the digitalisation of its power grids “brings new risks as [it] increasingly exposes the energy system to cyberattacks and incidents which may jeopardise the security of energy supply”.
In the meantime, the European Network of Transmission System Operators is preparing a Network Code on Cybersecurity, which aims to set a European standard for the cybersecurity of cross-border power flows. This includes rules on cyber risk assessment, common minimum requirements for the cybersecurity of critical infrastructure, cybersecure products and services, monitoring, reporting and crisis management.
In a global context of hybrid threats, Nato has also stepped up its efforts and integrated the security and resilience of critical energy infrastructure, as well as cyber threats, into its activities.
[Keep up with Energy Monitor: Subscribe to our weekly newsletter]
The security organisation founded an Energy Security Centre of Excellence in Vilnius in 2012, focusing on aspects related to military energy efficiency, and on the protection of critical energy infrastructure.
Ukraine became a member of this Centre of Excellence last year, and conducted a Nato-funded exercise on the protection of critical infrastructure and energy infrastructure in Odessa. Romualdas Petkevicius, the director of the Centre of Excellence, said on the day of Ukraine’s accession that “the accumulated experience of Ukrainians will be very useful for Nato and the Centre”.
“Ukraine has consistently built expertise and resilience in cybersecurity since 2015," says Sofiia Shevchuk. "Considering that even now, the large majority of critical telecommunications infrastructure is still working, one can see that cyber is another field where Ukraine keeps getting stronger and where it is able to confront Russia."
There are several challenges ahead, however, as the cyber threat ‘toolbox’ also becomes more sophisticated. “We have made some progress, but we have a long, long way to go,” says Butrimas.
“Many of the measures that we are taking to protect critical energy infrastructure are really based on long-established best practices of cybersecurity measures: protecting emails, protecting the websites… these do not apply very well or did not adequately apply to the industrial sector. In the industrial sector, we have a power grid, we have a hydroelectric dam, we have a power generation facility; your chief interest is in protecting the operation to make sure the physical process is kept in balance,” he adds.
An even-larger threat
The threat of major cyberattacks as a result of the Russia-Ukraine war has much of the EU worried, especially as the West has issued a strong response condemning Russia’s aggression.
This could embolden pro-Kremlin and Russian state-sponsored hackers. In the wake of the invasion, Politico reported that Russian ransomware gang Conti threatened to launch cyberattacks against countries retaliating against Moscow. Several EU and Nato countries have launched cybersecurity emergency response teams, formed by experts prepared to move to another country under attack within hours.
“In this respect, I think we have certainly improved our resilience,” Umbach says.
“But overall, despite raising the awareness on our side, despite having increased our defences and resilience, the [gap to the] capabilities of attackers, in particular state-supported groups, has still increased. We have made progress, but the attackers have too,” he sums up.
Nation-state or state-sponsored groups, known as Advanced Persistent Threats, continue to grow in sophistication. “They are maybe one or two steps ahead," says Butrimas. "So you might be planning a very IT-centric strategy to protect critical infrastructure, while the adversary has already gone past it."


